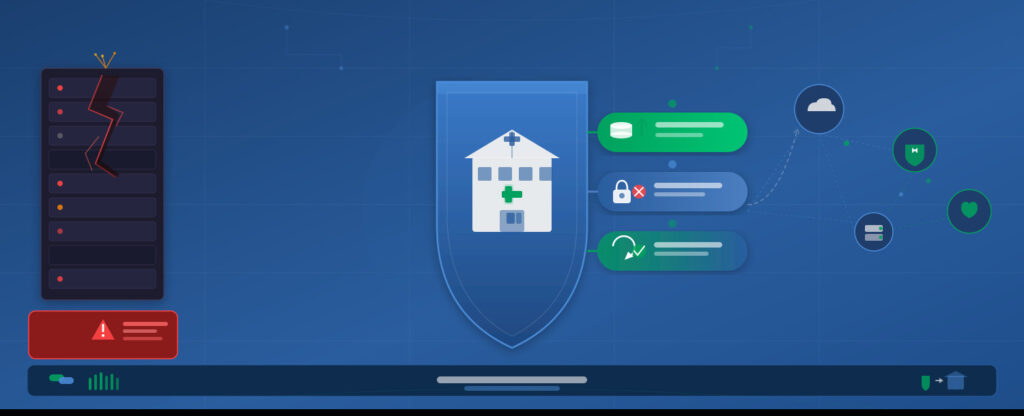
Healthcare is under attack — and the biggest threat isn’t medical emergencies, it’s cybercrime. With ransomware attacks rising 40% in 2023 (IBM Security), and AI risks rising exponentially by the day, patient data breaches are now the #1 risk for hospitals, clinics, and health systems.
The Department of Health and Human Services is proposing significant updates to the HIPAA Security Rule (part of the Health Insurance Portability and Accountability Act) to strengthen cybersecurity protections for Electronic Protected Health Information (ePHI) in healthcare and covered entities (like hospitals, insurers, pharmacies). This is driven by the escalating frequency and severity of cyberattacks targeting healthcare systems, which often lead to patient data breaches.
What’s New in the Proposed Rule?
HHS’ Notice of Proposed Rulemaking (NPRM) targets critical weaknesses in current HIPAA cybersecurity standards. Key changes include:
- Technical Safeguards
- Mandatory Encryption: Require strong encryption for all ePHI (both stored and transmitted)
- Multi-Factor Authentication (MFA): Enforce MFA for every system accessing patient data
- Network Segmentation: Mandate strict network boundaries to limit breach spread
- Vulnerability Management: Regular security testing and patching required
- Administrative Safeguards
- Enhanced Training: Quarterly HIPAA-compliant cybersecurity training for all staff (not just IT)
- Risk Analysis: More rigorous, real-time risk assessments for all systems
- Vendor Management: Clearer requirements for third-party vendors (e.g., cloud services)
- Incident Reporting
- Simplified breach definitions
- Faster notification requirements to patients and HHS
💡 Why this matters: These updates directly address threats like phishing, ransomware, and “shadow IT” — which cost healthcare organizations $9.2M per breach on average (2023 IBM Cost of a Data Breach Report).
Why This Isn’t Just “Another Rule”
This isn’t minor tweaking. It’s a revolution in HIPAA compliance:
- Patient Safety: Preventing data leaks from exposing medical histories or payment details
- Financial Risk: Avoiding fines and costly breach remediation
- Reputation: Trust is the bedrock of healthcare — breaches destroy patient confidence
- Legal Alignment: Future-proofing against evolving laws like the NIST Cybersecurity Framework
What You Should Do NOW
1. Audit Your Systems:
- Test encryption for ePHI
- Review access controls (especially for non-IT staff)
- Check vendor security contracts
2. Train Your Team:
- Conduct phishing simulations
- Document breach response protocols
3. Prioritize MFA: Ban single-factor logins across all patient-facing systems.
⚠️ Key Insight: This rule isn’t just for IT departments. Every clinician, nurse, and admin must understand their role in data security.
The Bottom Line
If implemented, the new HIPAA Security Rule is the most significant cybersecurity update in healthcare history.
Healthcare providers who prepare today will avoid fines, maintain patient trust, and keep their systems secure.
Don’t just comply — protect your patients and your business.







